Live Maps of Worldwide Ransomware and Cyber Attacks
There are a number of Live Maps that track Ransomware and Cyber Attacks around the world. These maps can be…
Top 10 Cybersecurity Threats in 2023
The following are the top 10 cybersecurity threats in 2023: 1. Cloud Vulnerability: As cloud storage becomes more popular, it…
What is LOLbins in Cybersecurity
What is LOLbins? LOLBins are legal Windows binaries that attackers can employ to accomplish malicious actions. They are frequently utilized…
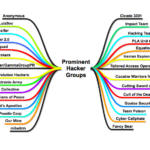
20 Ways to Learn Ethical Hacking for Free
Here are 20 ways to learn ethical hacking for free: 1. Root Me – Challenges Root Me is a platform…
What is Tunneling Protocol
What is Tunneling Protocol? A tunneling protocol is a network protocol that encapsulates one protocol’s data within the payload of…
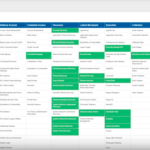
APT Group Trend – July 2023
To remain ahead of defenders, APT organizations are continually upgrading their tactics and strategies. The following are the cases of…
Tips and Precautions to take Against Ransomware
Ransomware is a sort of malware assault that encrypts files on a system, rendering the victim unavailable. The attacker then…
How Can I Keep My Company Safe from Cyberattacks?
Cyberattacks are becoming a more serious danger to organizations of all sizes. There were over 623 billion cyberattacks worldwide in…
The Importance of AI in Cybersecurity- Benefits and Precautions
When using AI in cybersecurity, it is critical to analyze both the advantages and drawbacks in order to maximize the…