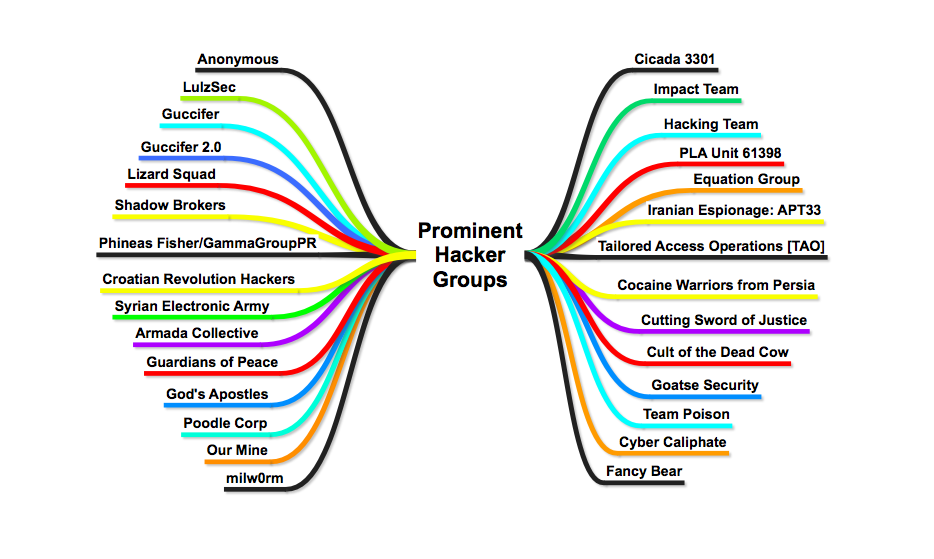
In this section we will discuss some of the most chaotic and prominent groups which are believed to be active till now
1. Anonymous
Anonymous is a loosely associated international network of activist and hacktivist entities. A website nominally associated with the group describes it as “an Internet gathering” with “a very loose and decentralized command structure that operates on ideas rather than directives”. The group became known for a series of well-publicized distributed denial-of-service (DDoS) attacks on government, religious, and corporate websites.
Anonymous originated in 2003 on the imageboard 4chan, representing the concept of many online and offline community users simultaneously existing as an anarchic, digitized global brain. Anonymous members (known as “Anons”) can be distinguished in public by the wearing of Guy Fawkes masks in the style portrayed in the graphic novel and film V for Vendetta. However this may not always be the case, as some of the collective prefer to instead cover there face without using the well-known mask as a disguise.
- One of the most famous hacker group and active since 2008 in various protests operations.
- Anonymous’ peak came arguably around 2010 and 2011, when the group launched a massive hacking operation in defense of WikiLeaks called Op Payback
- They made use of Internet for the largest protest via DDoS [Distributed Denial of Service] and Defacement with some the tools like
- LOIC: Low Orbit Ion Cannon (LOIC) is an open source network stress testing and denial-of-service attack application, written in C#
- Hoic: High-speed multi-threaded HTTP Flood : High Orbit Ion Cannon (HOIC), is an open-source network stress testing and denial-of-service attack application written in BASIC designed to attack as many as 256 URLs at the same time.
- Slowloris : The low bandwidth, yet greedy and poisonous HTTP client!
- Pyloris: PyLoris is a scriptable tool for testing a server’s vulnerability to connection exhaustion denial of service (DoS) attacks.
- Hping: hping is a command-line oriented TCP/IP packet assembler/analyzer.
4. Anonymous has four main goals which unite members. These are…
- anti-cyber-surveillance
- anti-cyber-censorship
- Internet activism
- Internet vigilantism
2. Cicada 3301
Cicada 3301 is a name given to an organization that on six occasions has posted a set of puzzles and alternate reality games to possibly recruit codebreakers/linguists from the public and listed as one of the “top 5 eeriest, unsolved mysteries of the internet” by The Washington Post. Cicada 3301, a kind of Internet scavenger hunt that relies on advanced code-breaking — and a working knowledge of things like obscure medieval literature and Mayan numerology — to unlock progressive clues. Who’s behind the puzzle is unclear, although many enthusiasts believe it’s a large, well-funded and shadowy organization trying to recruit into its membership.
- The first internet puzzle started on January 4, 2012, and ran for approximately one month.
- A second round began one year later on January 4, 2013.
- A third round following the confirmation of a fresh clue posted on Twitter on January 4, 2014.
- Cicada 3301 update: the baffling internet mystery is back
-
Cicada 3301: I tried the hardest puzzle on the internet and failed spectacularly
The stated intent was to recruit “intelligent individuals” by presenting a series of puzzles which were to be solved.
- No new puzzles were published on January 4, 2015. However, a new clue was posted on Twitter on January 5, 2016.
- In April 2017 another PGP signed message was found: Beware false paths. Always verify PGP signature from 7A35090F.
- Cicadas & Security, Part 2: When a Verified PGP Key Takes You on a Trip to the Desert
- That message explicitly denies the validity of any unsigned puzzle, as recently as April 2017.
3. APT 33
Recent investigations released a new threat actor named APT33 believed to be Prominent Iranian Hacker Group capable of espionage as well as spreading of one of the unseen species of malware called Wipers on the victims hard drive – once unleash capable of destroy data via wiping disks, erasing volumes and Deleting files depending on system’s configuration. We will be uncovering some of the facts and collective intelligence for the APT33 hacker group.
Insights into Iranian Cyber Espionage: APT33 Targets Aerospace and Energy Sectors and has Ties to Destructive Malware
- APT33 is a capable group that has carried out cyber espionage operations since at least 2013
- APT33 has shown particular interest in organizations in the aviation sector involved in both military and commercial capacities, as well as organizations in the energy sector with ties to petrochemical production.
- From mid-2016 through early 2017, APT33 compromised a U.S. organization in the aerospace sector and targeted a business conglomerate located in Saudi Arabia with aviation holdings.
- APT33 may have targeted these organizations as a result of Iran’s desire to expand its own petrochemical production and improve its competitiveness within the region.
- APT33 leverages popular Iranian hacker tools and DNS servers used by other suspected Iranian threat groups. The publicly available backdoors and tools utilized by APT33 – including NANOCORE, NETWIRE, and ALFA Shell – are all available on Iranian hacking websites, associated with Iranian hackers, and used by other suspected Iranian threat groups
- The ties to SHAPESHIFT may suggest that APT33 engages in destructive operations or that they share tools or a developer with another Iran-based threat group that conducts destructive operations.
4. OurMine Hacker Group
On Analysis, observing that OurMine made public appearance on Jan 2016 from Youtube accounts hijacks and then from May 2016 on roller coster ride of Twitter accounts hijacks which ride on serial basis till now making one by one Brand Defacements whether it may be Techie/ Celebrities Twitter Hacks or Famous websites Defacement or Leaking Data of Video Hosting Sites. Lots of reasons unknown about attack methodologies but No Doubt OurMine Group showed lots of variety in attack strategies from Twitter/Linkedin Accounts Hijacked to Data Stolen from Vevo , HBO.One theory states that, One of the Key reason for Celebrities twitter/ linkedin account takeover is re-use of exposed passwords in Linkedin password hack dated back in 2012, which was dumped partially on darknet and it could be a possibility that OurMine accessed it wisely.
Comments are closed.