As per press release statement released by Europol, The leader of the crime gang behind the Carbanak and Cobalt malware attacks targeting over a 100 financial institutions worldwide has been arrested in Alicante, Spain, after a complex investigation conducted by the Spanish National Police, with the support of Europol, the US FBI, the Romanian, Belarussian and Taiwanese authorities and private cyber security companies.
Since 2013, the cybercrime gang have attempted to attack banks, e-payment systems and financial institutions using pieces of malware they designed, known as Carbanak and Cobalt. The criminal operation has struck banks in more than 40 countries and has resulted in cumulative losses of over EUR 1 billion for the financial industry. The magnitude of the losses is significant: the Cobalt malware alone allowed criminals to steal up to EUR 10 million per heist.
Collective Intelligence Analysis
As per Kaspersky dubbed these actors as Carbanak authors and stated as
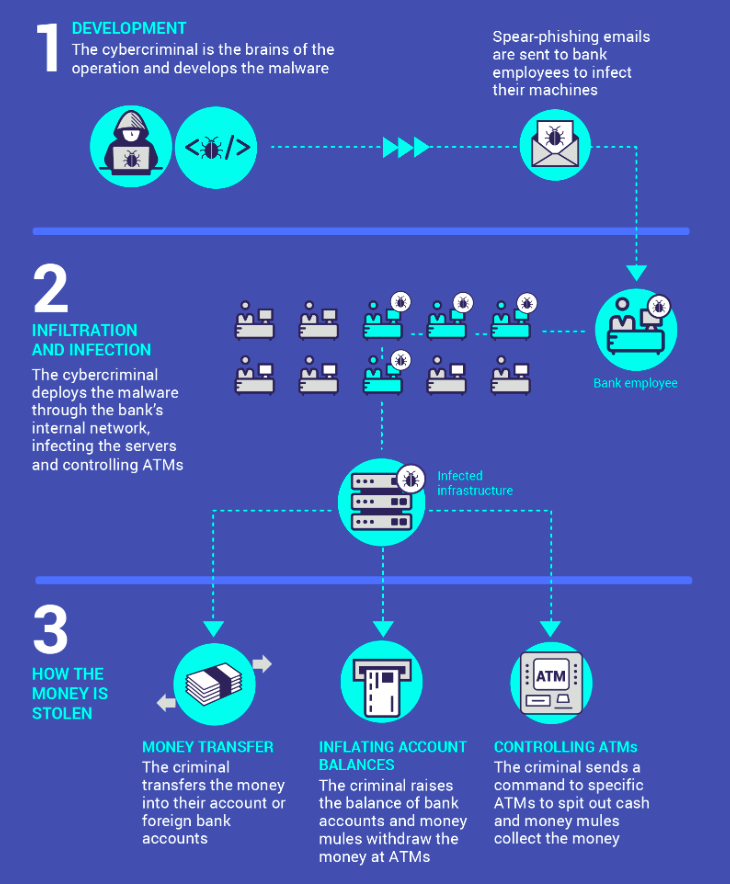
Kaspersky Lab, INTERPOL, Europol and authorities from different countries have combined efforts to uncover the criminal plot behind an unprecedented cyberrobbery. Up to one billion American dollars was stolen in about two years from financial institutions worldwide. The experts report that responsibility for the robbery rests with a multinational gang of cybercriminals from Russia, Ukraine and other parts of Europe, as well as from China. The Carbanak criminal gang responsible for the cyberrobbery used techniques drawn from the arsenal of targeted attacks. The plot marks the beginning of a new stage in the evolution of cybercriminal activity, where malicious users steal money directly from banks, and avoid targeting end users.
Since 2013, the criminals have attempted to attack up to 100 banks, e-payment systems and other financial institutions in around 30 countries. The attacks remain active. According to Kaspersky Lab data, the Carbanak targets included financial organizations in Russia, USA, Germany, China, Ukraine, Canada, Hong Kong, Taiwan, Romania, France, Spain, Norway, India, the UK, Poland, Pakistan, Nepal, Morocco, Iceland, Ireland, Czech Republic, Switzerland, Brazil, Bulgaria, and Australia.
Attack Detection and First Malware Sample containment
As per Kaspersky team, one of the colleagues received a call at 3 a.m. in the middle of the night from CSO of a Russian bank. One of their systems was alerting that data was being sent from their Domain Controller to the People’s Republic of China. On forensics investigation team was able to find the malware on the system and encountered the Carbanak malware for the first time by writing a batch script that removed the malware from an infected PC and ran this script on all the computers at the bank to collect the samples.
Modus of Operandi
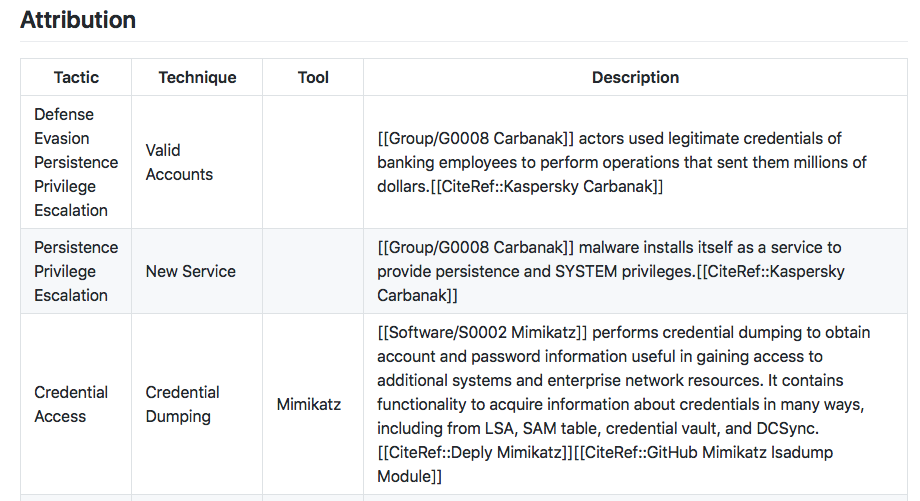
As per resports analysis by ISACA rome chapter, Carbanak has launched campaigns attempting to:
- Target high level executives in financial companies or in financial/decision-making roles in the Middle East, U.S. and Europe
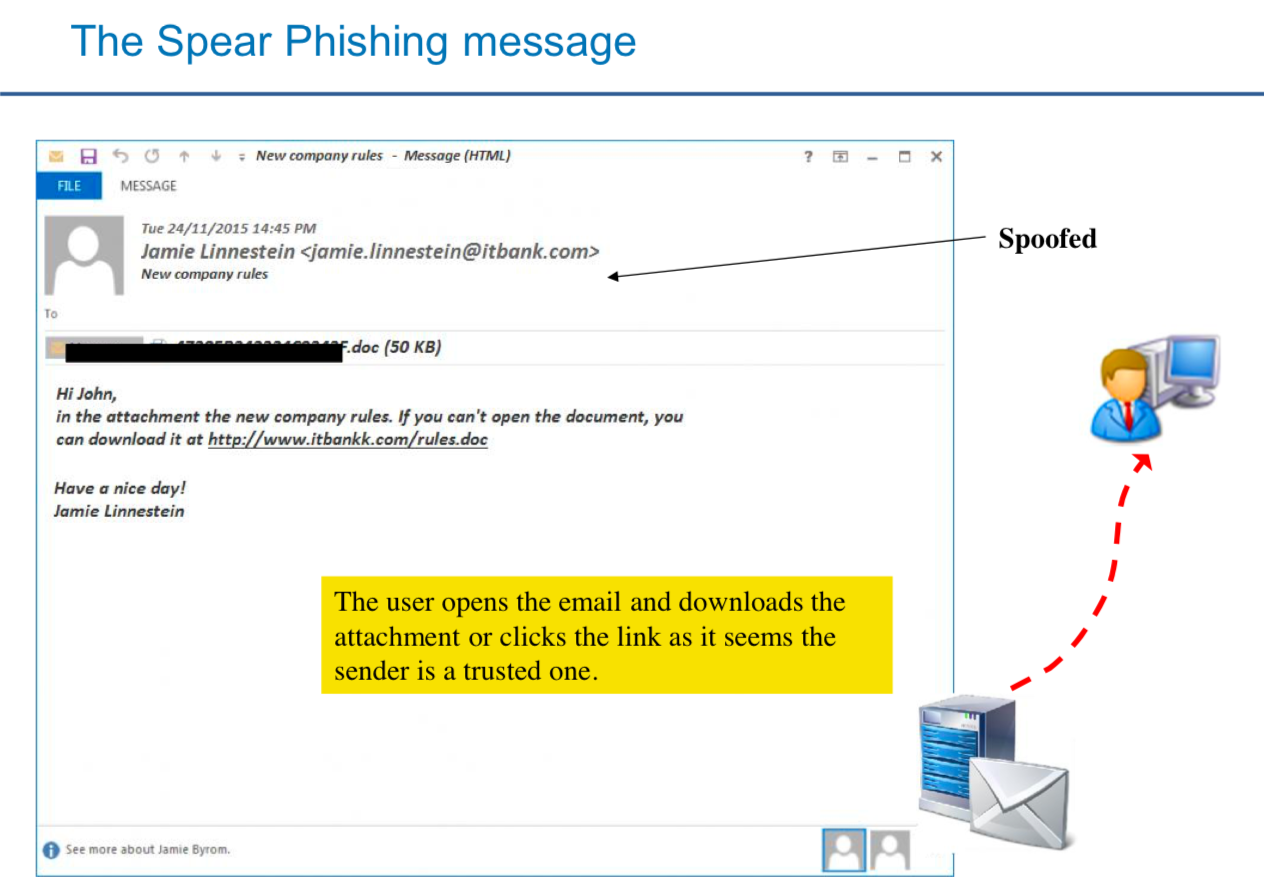
- Spear-phishing emails delivering URLs, macro documents, exploit documents
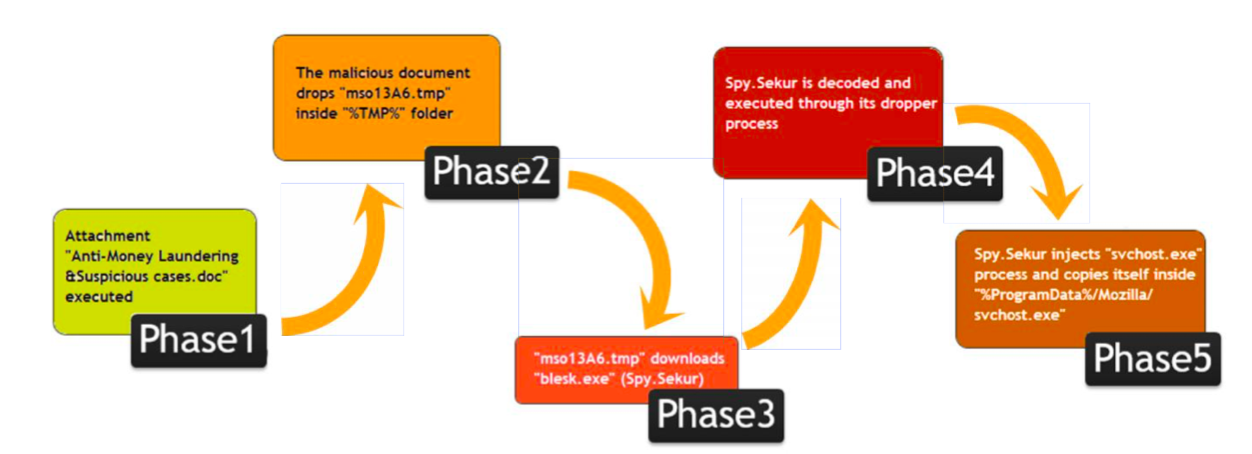
- Use of Spy.Sekur (Carbanak malware) and commodity Trojans (RATs) such as jRAT, Netwire, Cybergate, but also others software used to support the crew operations.
- Since 2014, Carbanak has integrated ATM malware to his arsenal making the group one of the most threatening for the entire financial sector.
The sequence of attacks can be highlighted as below [ derived from ISACA report]
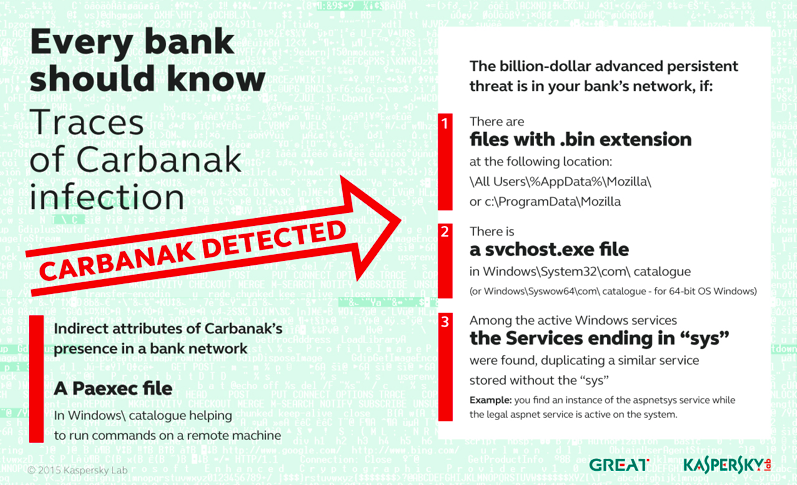
IOC Detection and prevention methods
Threat Hunting – Github Repository for Carbanak Malware adversary_attribution
Github Repository – source Cyb3rWard0g/ThreatHunter-Playbook
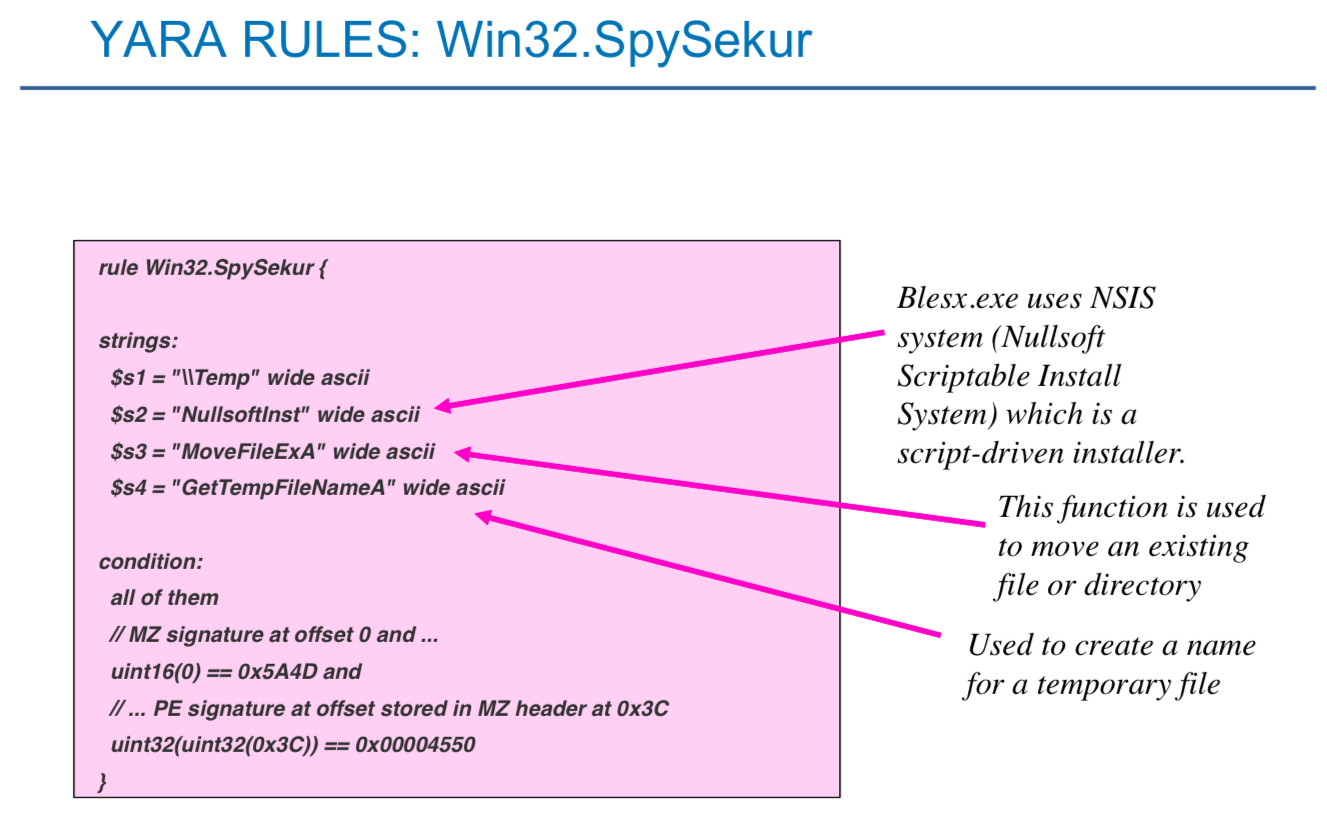
Yara Rules for Detection
Research Reports and Analysis
- 13 October 2013 – THE CARBANAK/FIN7 SYNDICATE A HISTORICAL OVERVIEW OF AN EVOLVING THREAT – Whitepaper analysis
- 19 January 2015 – Carbanak or Anunak Threat Advisory by Secure Data
- 16 February 2015 – APT REPORTS The Great Bank Robbery: the Carbanak APT – Kaspersky Lab Analysis
- 5th July 2016 – Carbanak: Introduction Modus Operandi Strategy of Remediation – Analysis by ISACA Rome chapter
- October 2017 – Carbanak Threatens Critical Infrastructure Cybercriminal APTs Merit Significant Investigation and Discussion report
- AnunAk: APT AgAinsT finAnciAl insTiTuTions – Group-IB and Fox-IT Report
- 10 October 2017 – FIN7 group which is closely tied to the notorious Carbanak Gang – Analysis report by Morphisec
- 2016/2017 – The National Threats to UK business – Analysis report by National Crime Agency.